 If you are anything like me, historically your initial discussions with IT drifts toward their requirements and policies- some version of a C-I-“No”. This is usually followed by some type of business-sponsor intervention allowing us to technologically enable our business outcome, with at least a little lingering animosity. During a recent webinar1, Professor George Westerman of MIT’s Sloan Center for Digital Business says it doesn’t have to be this way.
If you are anything like me, historically your initial discussions with IT drifts toward their requirements and policies- some version of a C-I-“No”. This is usually followed by some type of business-sponsor intervention allowing us to technologically enable our business outcome, with at least a little lingering animosity. During a recent webinar1, Professor George Westerman of MIT’s Sloan Center for Digital Business says it doesn’t have to be this way.
Professor Westerman’s belief is the conflict between the business strategic outcome and IT’s natural resistance to manage and maintain the changes and exceptions into perpetuity can be addressed by:
- thinking about IT’s risk, and
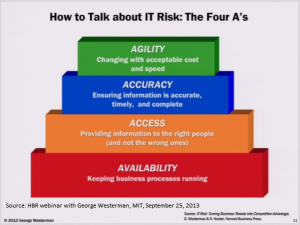
- focusing a dialogue with IT on the four A’s (Availability, Access, Accuracy, Agility)
 The Four A’s
The Four A’s
The four A’s (click on exhibit How to talk about IT Risk: The Four A’s) seem like a very rational place to start a technology enablement discussion. Initial dimensions center a business-technology discussion around the tradeoffs of business outcomes, service level agreements (SLAs), and potential risks. By focusing on these types of risk, Westerman posits, we get away from discussion of security, policy, vetoes, “no” and “can’t” to alternatives and managing risk. Increasing understanding and getting risk built into every conversation should be the goal.
A risk based system
The four A framework functions within a system of “good governance platform”, a foundational technical platform “fit for purpose”, a risk aware culture, and internal communication to facilitate collaboration. Westerman also discussed six key factors2 to start the transformation to a risk based system.
- Talk and think differently about IT risk management
(e.g., Use the four A framework to assess each business process) - Use the risk governance process to improve IT, not just protect it
(e.g., Does business continuity inform multiple areas?) - Promote a risk-aware culture
(e.g., Does risk management support business excellence?) - Break down silos inside IT
(e.g., Can we use risk to frame infrastructure improvements?) - Be ready for new technologies
(e.g., What alternatives exist?) - Make risk management part of strategic discussions
(e.g., Is there a better way?)
The bottom line
Start the dialogue with IT. I look forward to using the four A’s next chance I get.
End Notes and References
1 “IT Risk: The conversation you must have now”, Harvard Business Review Webinar, September 25, 2013, featuring Professor George Westerman, Research Scientist, MIT Center for Digital Business [internet]. Also see Professor Westerman’s books IT Risk: Turning Business Threats Into Competitive Advantage (2007) with and The Real Business of IT: How CIOs Create and Communicate value (2009) both co-authored with Richard Hunter and published by Harvard Business School Press, Boston.
2 This listing is summarized from two slides “How to start your transformation” presented during the “IT Risk: The conversation you must have now”, Harvard Business Review Webinar, September 25, 2013 [internet]. Sub-bullets from the presentation have been edited to one example for clarity.

